
Are You Reacting, or Are You Proactive?
How much does it really cost to deal with IT issues as they come up instead of taking a proactive approach? We explore that in today's article.

How much does it really cost to deal with IT issues as they come up instead of taking a proactive approach? We explore that in today's article.

How does a woman willingly hand her keys over to a car thief? How do employees willing hand over account credentials to a cyber criminal? Find out in this article.

Coaxing as much life as possible out of your hardware sounds like a good idea on the surface, but what is it actually costing you?

Passwords are important, but they really aren't enough. In this article, we examine the use of Multi-Factor Authentication as an extra tool in protecting your online accounts.

Old passwords on long forgotten accounts, reused "perfect" passwords, all this and more put you at risk today.
Anti-virus. We all understand it's needed, but do we truly understand how it works? Here we break down how traditional AV works and why it simply isn't enough for the modern threat landscape.
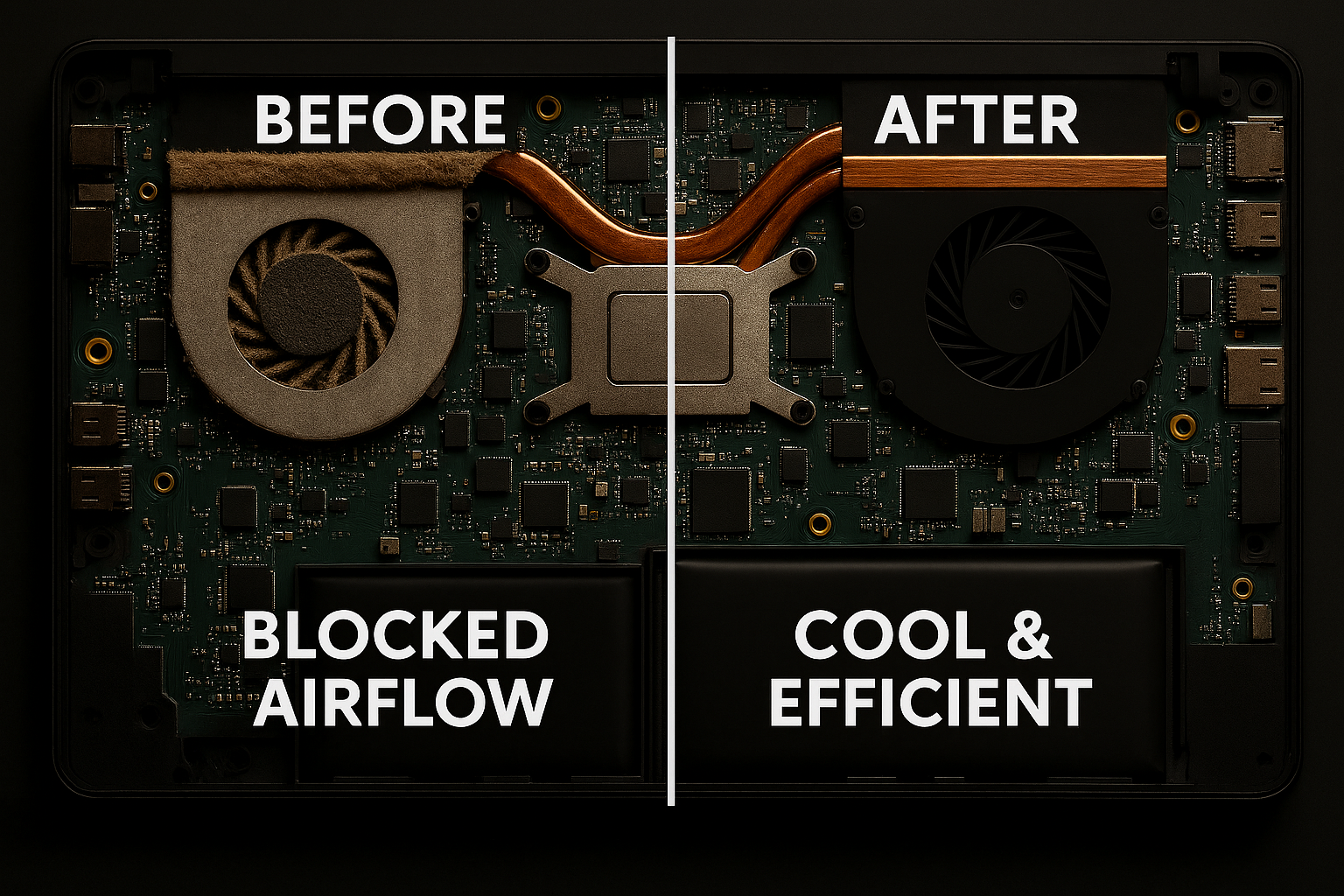
Spring Cleaning for Your Silicon: A Northern Utah Tech Guide

We're excited to announce our new MDM services for businesses looking to secure and manage their mobile fleet. Contact us to learn more about keeping your team's devices safe and organized.